Ransomware Attacks Against SaaS Data: 4 Security Measures to Take Now
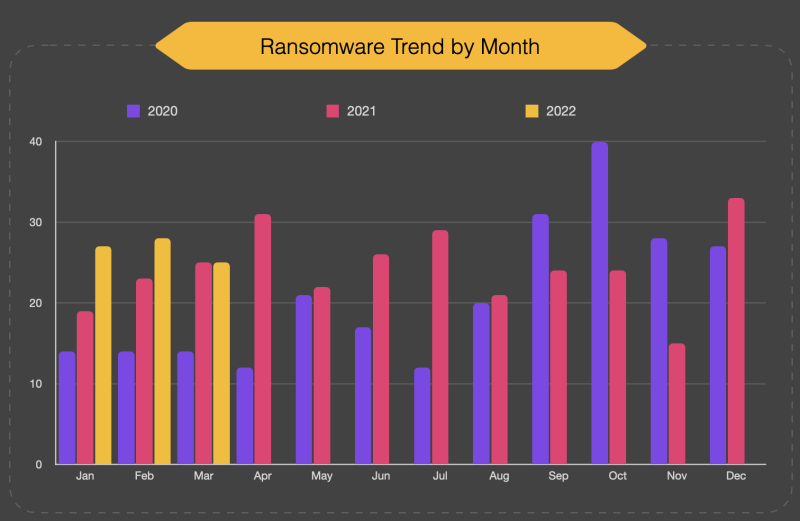
Ransomware attacks are on the rise, jumping up 62% between 2020 and 2021.* At the same time, enterprises are increasingly adopting cloud infrastructure for mission-critical business processes, collecting and distributing sensitive customer and transactional data within SaaS programs like Salesforce.
So it's no surprise that ransomware attackers have shifted their targets to SaaS data. These catastrophic attacks force companies to either pay wildly expensive ransom payments or lose critically-important business data.
Enterprises need to be aware of the risks of a ransomware attack on the data they store in the cloud, and be prepared to detect malicious activity, interrupt an attack, and recover affected data to avoid embarrassing, expensive business interruptions.
Here are the risks that can lead to a ransomware attack on an organization’s Salesforce data, and four security measures that can prevent, stop, and remediate them.
Note: Register for our May 18 webinar "How to Protect your SaaS Data from Ransomware Attacks" here!
Understanding the risk of a ransomware attack on Salesforce data
Ransomware attackers are opportunists. They follow market rules, which means they choose the most optimal balance of effort versus potential revenue. For that reason, Salesforce itself is a highly unlikely potential victim of a ransomware attack because bypassing the platform's strict technical controls is simply too difficult.
But just because your organization runs on a platform as secure as Salesforce doesn't mean that your organization’s Salesforce data won't be the target of a ransomware attack.
How? Attackers may gain access to credentials through phishing techniques, malware installed on a user's device, API key leaks, or other malicious methods. Attackers can then use the Salesforce API to export the data and overwrite it with an encrypted version. To obtain the decryption key, victims must then pay a ransom in return. Victims will pay to avoid material damage to the company, including business interruption, fines for non-compliance with data security laws that could have prevented the attack, reputational impact, etc.
And since your organization is responsible for your data - not Salesforce - you need to protect data against such an event. Leaders at many organizations do not realize this. According to a recent ESG research report, 35% of IT leaders mistakenly believe their cloud vendor (such as Salesforce) is responsible for protecting their data.** As a result, they are not taking the necessary security measures to protect end-user device security, cloud login credentials, or vet third-party applications - all of which leave the organization vulnerable to a ransomware attack.
Now that you understand the risks, let's explore the proactive and reactive security measures your organization can take to prevent and minimize the effects of a ransomware attack on Salesforce data.
4 security measures that protect against ransomware attacks
Attackers seek out target companies using SaaS applications that support critical business activities, especially when the victim organization may not have realized the shared responsibility model for cloud security (and therefore the measures that need to be put in place).
These are the security measures to put in place:
1. Leverage Salesforce's built-in security tools:
First and foremost, leverage the built-in security tools offered by Salesforce, including Transaction Security, outlined here. When a suspicious event occurs, you should create policies to block the requested action and send alerts to your team.
2. Detect a ransomware attack with Salesforce data monitoring tools:
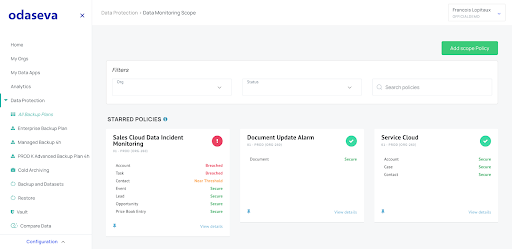
The sooner you detect a ransomware attack, the sooner you can stop it, and the easier it will be to recover from. Tools like Odaseva Monitoring powered by Tableau CRM (Einstein Analytics) can detect ransomware attacks in progress by:
- Monitoring critical objects for Insert, Update, & Delete events, and
- Setting thresholds for your most critical objects and send email alerts to your administrators when thresholds are reached
By getting alerted when there's unusual activity on your Salesforce data, you can investigate and react as necessary.
3. Have visibility into what data was impacted:
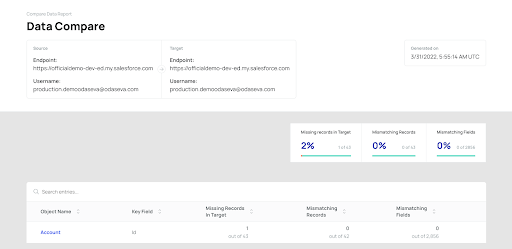
You detected and interrupted a ransomware attack. Now you need to know what data was impacted so you can restore the right data - quickly.
A tool like Odaseva Data Compare helps you easily and quickly identify which objects, fields, or records have changed. Then you can restore the affected data from a backup.
4. Have the ability to recover your data:
Backup your Salesforce data as frequently as necessary, depending on the criticality of the objects. But know that it's just as important to ensure your backups can be restored!
Run restore tests regularly to identify any potential roadblocks to a speedy and effective data restoration (note: this is crucial for any Disaster Recovery Plan - not just ransomware attacks). This will get you up and running faster - preserving revenue and improving the customer experience.
How Odaseva can help:
As the leading Enterprise Data Platform for Salesforce, Odaseva offers powerful tools to keep Salesforce data protected against ransomware attacks and other business continuity threats.
We’re hosting a webinar on May 18, 2022 called "How to Protect your SaaS Data from Ransomware Attacks." Register now here to learn:
- The risks that can lead to a ransomware attack on an organization’s Salesforce data
- Security measures that can prevent, stop, and remediate ransomware attacks
- How Odaseva can help protect against ransomware attacks and other business continuity threats
If you can't attend the live webinar, register anyway and we'll send you the recording. You can also get in touch today for a personalized demo here.
* Source: The State of Ransomware in 2022, Blackfog
** Source: 2021 Data Protection Cloud Strategies, The Enterprise Strategy Group, 2021
View other stories

Odaseva for Agentforce: How to Give Access to Archived Data

What Do Architects Say About the Salesforce Ecosystem? Key Insights from the 2025 Salesforce Ben Survey





